LinkedIn verification: secure? Realiable? Think again.
Examining biometric processing, subprocessor chains, CLOUD Act exposure, and data sovereignty risks for users and organizations.

Globally speaking, January recorded 722 publicly claimed victims (verified).
February rose slightly to 782 claims, highlighting a strong trend.
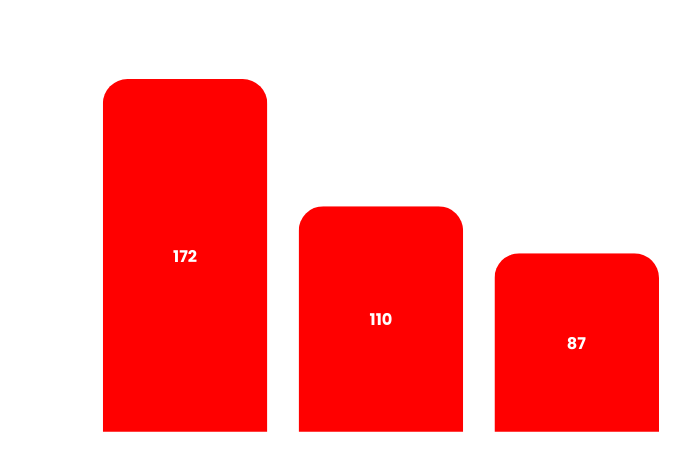
January recorded 20 confirmed claims affecting organizations across multiple sectors.
In February, incidents rose to 26, reflecting only cases that were fully validated and confirmed.
Monitoring ransomware activity demands a careful balance between comprehensive coverage and analytical rigor. Our monitoring focuses exclusively on ransomware groups whose claims can be considered credible and attributable to identifiable targets.
Entities operating primarily as data brokers, aggregators of previously leaked material, or actors publishing unverifiable claims are excluded from our dataset, as their activity does not reflect genuine ransomware operations.
It is also common for certain groups—particularly those emerging from hacktivist environments—to adopt ransomware-style extortion tactics. In these cases, we evaluate the claims themselves rather than relying solely on the group’s declared identity.
Each incident is subject to manual verification, duplicate detection, and contextual analysis. Claims that cannot be verified or cannot be linked to a legitimate and identifiable target are excluded from monitoring and statistical analysis.
ransomNews is an independent observatory dedicated to tracking and analyzing global ransomware activity. We monitor cyber extortion claims across the world, verify each incident manually, and compile clear, data-driven insights with a sharp focus on Italy.
Every month, we publish RedACT, in-depth report to inform, educate, and raise awareness - empowering businesses, institutions, and individuals to better understand the evolving ransomware landscape.
Our mission: to turn raw data into actionable knowledge, making cybersecurity a shared responsibility.
RedACT & dataset

Examining biometric processing, subprocessor chains, CLOUD Act exposure, and data sovereignty risks for users and organizations.

A technical analysis of landmark ransomware attacks, examining operational impact, state response, critical infrastructure risk.

An evidence-based analysis of supply chain ransomware vectors and threat actor evolution, sector exposure.

One of the most discussed ransomware group seems in between: a rising star in the RaaS ecosystem or a mass fake effect?

Another breach at one of the most known university in Italy and abroad; could be tied to Spain and US incidents?

The quiet moment when an assistant stopped asking and started acting, and a whole social network shaked the buzz

Strategically critical, technologically messy, and yet many serious incidents land with a dull thud in public awareness.
We monitor ransomware claims published by threat actors, verify their credibility, and enrich the data to provide structured intelligence on global ransomware activity.
We compile RedACT and RedACTinsights, free resources offering rigorously verified, data-driven reporting on ransomware activity and threat actors.
We support organizations and institutions with tailored ransomware intelligence reports, sector-specific and data-driven.
We deliver curated threat landscape briefings, sector-specific, timely, and actionable, relevant to any organization.
Awareness
We raise awareness around invisible exposure: how our digital habits, overlooked traces, and public signals can silently map our vulnerabilities.